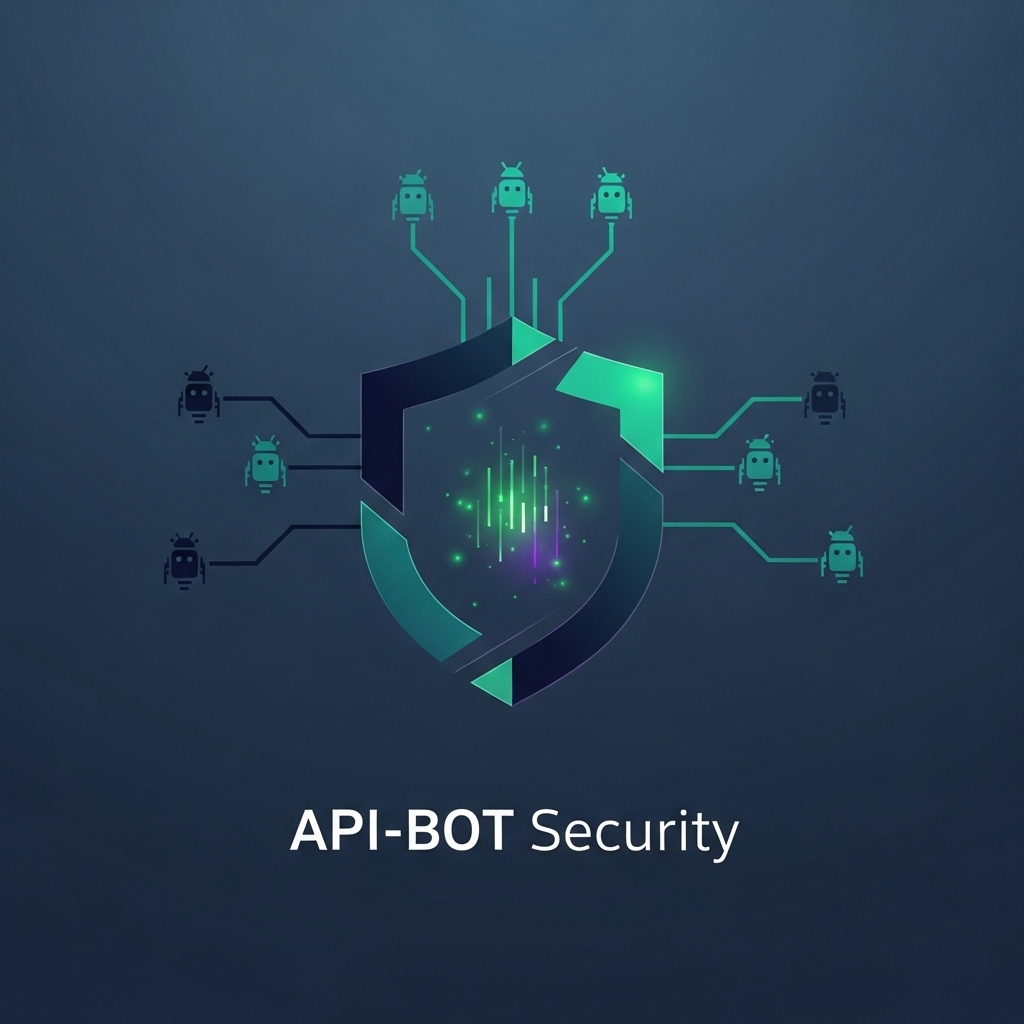
API-BOT Security
API-BOT security encompasses the set of technologies and best practices designed to protect an organization’s APIs and applications from malicious bots and cyber threats. APIs serve as critical interfaces for data exchange and service delivery, and as such, are attractive targets for abuse and exploitation.
Key Components of API-BOT Security
Authentication and Authorization:
Robust authentication mechanisms like OAuth 2.0 and OpenID Connect verify the identity of users and bots accessing APIs. Fine-grained authorization policies ensure that users only access resources appropriate to their roles.
API Keys and Token Management:
API keys and tokens provide a secure way to identify and track API consumers. Proper token lifecycle management, including expiration and rotation, is essential for reducing the risk of misuse.
Rate Limiting and Throttling:
To prevent abuse and resource exhaustion from malicious bots, rate limiting and quota controls are enforced. These measures help maintain service availability and performance.
API Web Security Controls:
Web Application Firewalls (WAFs), TLS encryption, payload validation, and threat filtering offer an additional layer of protection for API endpoints.
Malicious Bot Detection:
Behavioral analytics and machine learning models can detect abnormal request patterns and differentiate between human and bot traffic. Techniques include analyzing user agents, IP reputation, and session behavior.
Logging and Monitoring:
Comprehensive logging of API calls, including request metadata and response statuses, is critical for detecting anomalies and facilitating forensic investigations. Integration with SIEM platforms enhances threat detection.
Data Encryption:
Sensitive data transmitted via APIs must be encrypted in transit (via TLS) and at rest. End-to-end encryption is especially important for protecting personally identifiable information (PII) and financial data.
Security Testing and Continuous Assessment:
Regular vulnerability assessments, penetration testing, and automated scanning help identify and remediate weaknesses in API implementations. Ongoing testing ensures that security keeps pace with development.
Why API-BOT Security Matters
APIs are the gateways through which external systems interact with organizational services. If left unsecured, they expose critical systems to a wide range of threats including service disruption, data breaches, fraud, and abuse by malicious bots.
A robust API-BOT security strategy not only safeguards data and services but also ensures a reliable, secure, and seamless user experience for legitimate consumers.