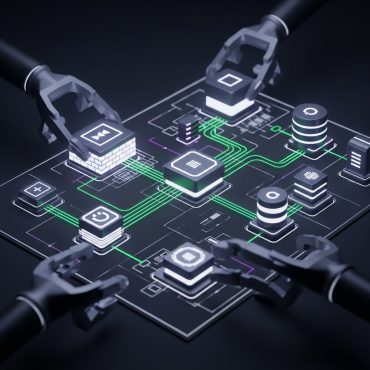
Secure System Architecture Design
In an era where cyber-attacks are increasingly sophisticated and persistent, embedding security into the core of your system architecture from the outset is far more effective than taking reactive measures. Kutsec’s Secure System Architecture Design service offers a proactive approach to ensure organizations build cyber-resilient, scalable, and reliable systems. This [...]